《鄉民大學問EP.38》直播|你反廢死嗎?歡迎來戰!廢死憲法法庭激辯!公投決定你支持?藍黨團提520後 邀賴清德立院國情報告!韓國瑜將正面對上 藍綠攻防?|NOWnews
NOW影音
更多NOW影音焦點
更多焦點-

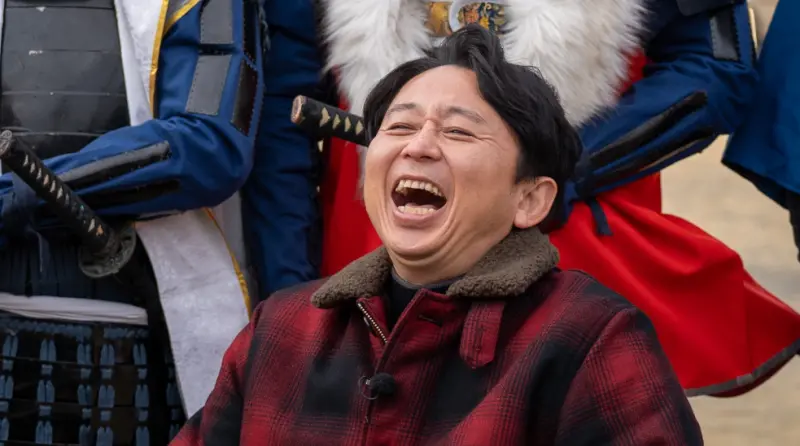
立院接見美國僑胞團!韓國瑜「突冒1句虧立委」 台下全笑翻
立法院長韓國瑜24日在立法院接見美國僑胞團,他於致詞時表示,現在立院三黨不過半,紛紛擾擾、吵吵鬧鬧,不過卻透過攻防,感受到台灣民主一步步的進步,他也開玩笑表示「現在三黨立委看到華僑回來都笑咪咪,各位華
2024-04-25 09:16
-

Meta盤後股價崩16%、美股盤前期指走低 台股遇壓開盤失守2萬點
美國股市昨(24)日漲多於跌,不過Meta受到亂流盤後股價大跌16%,拖累美股盤前期指今(25)日走跌,連帶也影響到台北股市開盤情形,下跌172.57點、來到19959.17點,失守兩萬點關卡,預估成
2024-04-25 09:02
-

《淚之女王》金智媛結婚現場!韓劇CP御用飯店 玄彬孫藝真也愛這
金秀賢、金智媛搭擋的Netflix韓劇《淚之女王》,開播後一路維持高收視率,目前距離tvN電視台收視率第一的紀錄僅一步之遙。本週末《淚之女王》將播出完結篇,讓不少粉絲都十分期待金秀賢與金智媛這對CP可
2024-04-24 17:39
-

屏東男酒駕撞5車!7旬婦人「馬上到家」慘遭撞死 再釀5人受傷
屏東萬丹鄉24日發生死亡車禍,41歲楊男酒駕上路,行經萬順路二段與南北路一段路口時,追撞正在停等紅燈的3輛自小客與2輛汽車,造成騎機車的老婦送醫不治,還有5人受傷。據了解,死者陳黃姓婦人(70歲)當時
2024-04-25 09:03
精選專題
要聞
更多要聞-
「賴皮寮」只有17萬?王鴻薇打臉賴清德揭穿2大謊言:失信於民
準總統、民進黨主席賴清德昨日在民進黨中執會中透露,萬里老家經過新北市政府鑑價、僅是價值17萬的房屋,所以「價值太低、無人可以承作。」國民黨立委王鴻薇指出,這荒謬的謊言說出口,網路上罵聲不斷,更有不少人
2024-04-25 09:09
-

沒廢死但上次槍決已是4年前!扁、馬、蔡執政24年 67死刑犯伏法
憲法法庭前天審理死刑是否違憲案,進行言詞辯論,主要討論爭點包含死刑是否違憲以及若合憲、違憲的相關配套措施,並由12位大法官參與投票,最快將在7月下旬做出判決。台灣現在雖然沒有廢死,不過事實上,上次政府
2024-04-25 07:30
-

民進黨為何要廢死?8年槍決2死囚 蔡英文、賴清德談死刑說法曝光
憲法法庭昨審理死刑是否違憲案,進行言詞辯論,主要討論爭點包含死刑是否違憲以及若合憲、違憲的相關配套措施,並由12位大法官參與投票,最快也將在7月下旬做出判決。民進黨2016年上台後,雖曾槍決2死囚,但
2024-04-25 07:00
-

黃偉哲不做滿為幫某人助攻南市長?賴清德向陳亭妃保證:不可能
民進黨地方黨部主委改選競爭激烈,牽動2026年縣市長佈局。民進黨立委陳亭妃今(24)日臉書指出,近來一直有人在台南放一種聲音說,台南市長黃偉哲不會做滿任期,會由中央派代理市長,專心爲某人的初選助攻,她
2024-04-24 21:22
新奇
更多新奇-
被《關鍵時刻》誤認成東大教授!有吉弘行看到了 本人回應超幽默
台灣政論節目《關鍵時刻》,由知名主持人劉寶傑領銜,時常針對各種時事進行語氣激昂的講解。不過近期在談論423地震話題時,誤將日本知名諧星主持人有吉弘行當成日本東京大學地震權威教授笠原順三,截圖瞬間在網路
2024-04-24 22:31
-
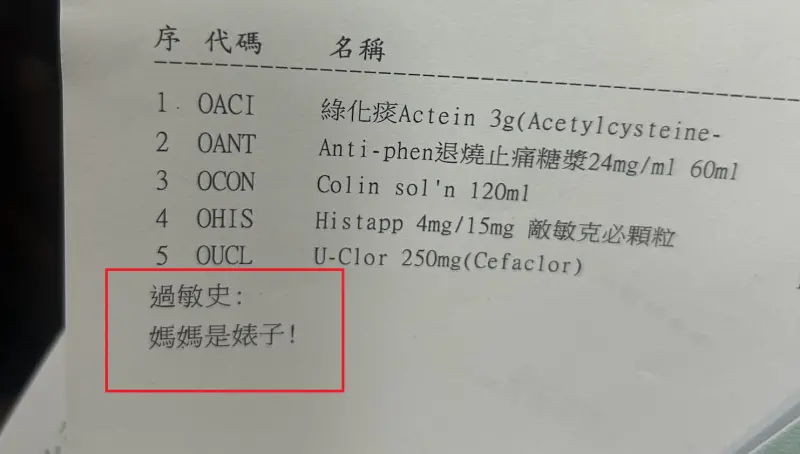
基隆醫院藥單上標註「媽媽是婊子」!人妻一看傻眼 護理師急道歉
(更新時間10:10)一位媽媽今(24)日帶著孩子前往衛生福利部基隆醫院看診,沒想到拿到藥單時,卻看到上面過敏史竟寫上:「媽媽是婊子!」讓她當場傻眼,詢問醫院究竟是怎麼回事,護理師同樣納悶,也立刻向她
2024-04-24 21:09
-

世界100大美食最新排行曝光!台灣竟成「吊車尾」:連英國都輸了
許多國際遊客來台一定會品嘗珍奶、小籠包、雞排、滷肉飯,甚至勇敢一點的還能嘗試看看臭豆腐。卻有國際美食榜單,將台灣美食排名列在榜單末端,甚至還有頗具權威性的美食評論刊物,2023年度最新榜單只給台灣第7
2024-04-24 18:43
-

全聯「稀有水果4顆99元」!隱藏福利曝:送保鮮盒 眾錯過再等1年
先別管60元便當了!全聯福利中心因為經常推出許多新品,或者是期間限定的產品,因此婆媽常常會在臉書社團上討論分享。然而近日就有不少人分享去全聯購買「寶石紅奇異果」,並且開箱分享口感,沒想到卻釣出內行婆媽
2024-04-24 18:29
娛樂
更多娛樂-

吳淡如估「理髮師月入12萬」比教師薪水高!揭現實面:AI不易取代
59歲知名作家吳淡如去年到大陸湖南大學攻讀歷史博士,常在社群上分享當學生的日常。22日她分享在當地巷內理髮店剪頭髮的經驗,花了20分鐘只要台幣180元,她也試著推算兩個師傅的薪水,「每個月收入可能有台
2024-04-25 08:16
-

《康熙來了》女星罹乳腺癌!無數夜晚難眠 淚崩痛訴:已切除右乳
48歲日籍女星小林優美曾來台發展,1999年發行的專輯《Why》排行台灣銷量第二名,還常時常登上節目《康熙來了》。日前小林優美在社群上發文,透露自己得了「乳腺癌」,她難過表示,「自從得知罹患乳腺癌後,
2024-04-25 07:44
-

孔劉、宋慧喬「夢幻搭檔」!傳加盟超強金牌編劇新作:陣容超豪華
孔劉今(24)日被爆將與宋慧喬2人共同主演由南韓金牌編劇盧熙京所寫的新作品。過去,盧熙京曾打造出《我們的藍調時光》、《Live》、《世上最美麗的離別》、《那年冬天風在吹》、《沒關係,是愛情啊》等經典作
2024-04-24 22:22
-

傳賣梁朝偉香港3億豪宅「海賺9千萬」 劉嘉玲獲讚理財有方
香港女星劉嘉玲日前才剛曝光上海的5億豪宅,近日又被香港媒體報導要將持有13年的4房豪宅以7380萬元港幣(約3億1011萬元台幣)的價格賣出,獲利超過2100萬港幣(約8855萬元台幣),讓不少粉絲都
2024-04-24 21:01
運動
更多運動-
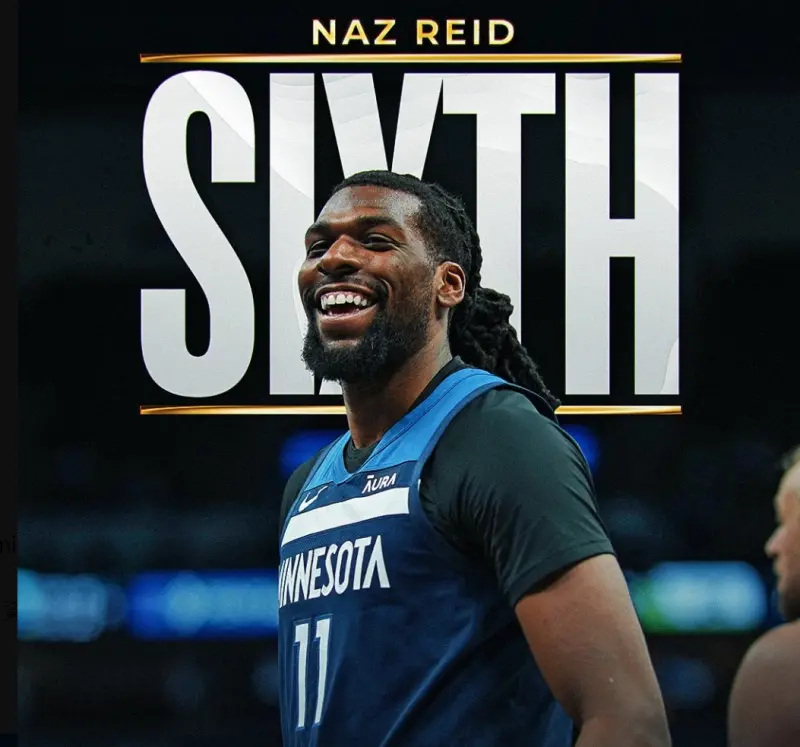
NBA年度最佳第六人出爐!落選秀、灰狼Naz Reid當選 成史上第3人
NBA美國職籃在今(25)日宣布2023-24賽季年度最佳第六人,明尼蘇達灰狼隊Naz Reid以10分之差,拿下年度最佳第六人,成為自1999年Darrell Armstrong以來,史上第3位未經
2024-04-25 08:26
-

4/25NBA季後賽搶先報/SGA領軍雷霆拚2連勝!熱火力尬塞爾提克
2024NBA季後賽第二輪賽事,4/25日上午7時將由邁阿密熱火客場出戰「綠衫軍」塞爾提克,而第二場西區賽事奧克拉荷馬雷霆9:30分將出戰紐奧良鵜鶘,塞爾提克今年一樣拿到東區第一,主場在 TD Gar
2024-04-25 07:33
-

中職快評/老鬼正夯!42歲雙雄潘威倫、林智勝還能締造多少歷史?
中華職棒今年焦點之一,絕對是42歲投打雙雄潘威倫和林智勝,今年最後一舞,能締造多少紀錄。套句球迷老話,「看一次,少一次!告別倒數計時。」繼日前統一獅潘威倫中繼拿下149勝之後,味全龍「大師兄」林智勝也
2024-04-25 04:12
-

NBA快評/太陽崩盤三大主因 Booker被爆賽前找「玩偶姊姊」紓壓
季前被視為是奪冠大熱門的太陽,在季後賽首輪苦吞二連敗,且華麗「三核心」進攻組合Devin Booker、Kevin Durant、Bradley Beal似乎有心無力,連兩戰團隊得分都未達100,且輸
2024-04-25 04:10
財經生活
更多財經生活-
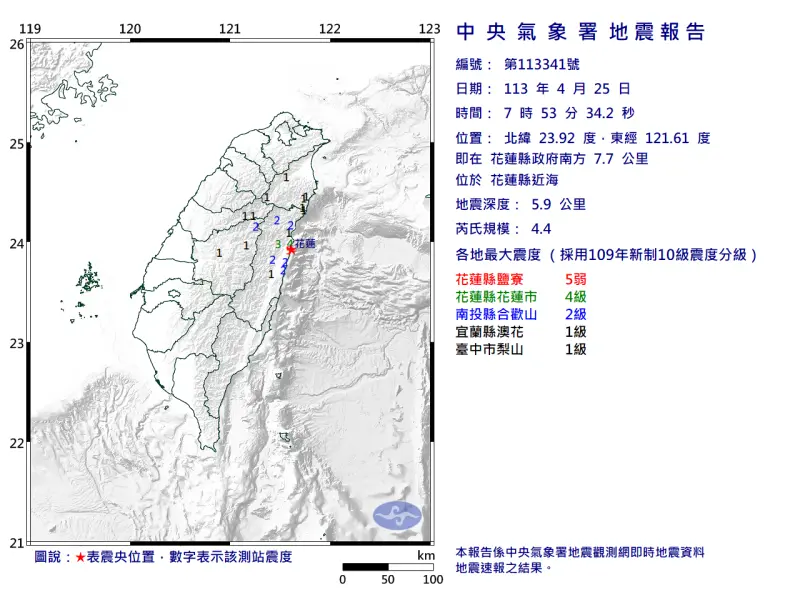
快訊/花蓮7:53「26分鐘連3震」!最大震度5弱 3縣市有感搖晃
今(25)日凌晨2時11分才發生規模5.6地震,一早再度地牛翻身,上午7時53分發生規模4.4地震,地震深度5.9公里,震央位在花蓮縣政府南方7.7公里(花蓮縣近海),最大震度為5弱,出現在鹽寮區。上
2024-04-25 08:36
-

鋒面襲台雨彈狂炸!「10縣市」發布大雨特報 大雷雨猛灌這3地
今(25)日因鋒面接近影響,苗栗至屏東地區有局部大雨發生的機率,中央氣象署一早6時55分針對10縣市發布大雨特報,台南市、高雄市、屏東縣則發布大雷雨即時訊息,提醒民眾注意雷擊及強陣風,山區慎防坍方及落
2024-04-25 08:06
-

限3天快搶!全家美式、霜淇淋「第2件10元」 7-11整瓶烏龍茶10元
全家週末分享日優惠提早曝光,4月26日起有特濃美式、仙女紅茶第2杯10元,霜淇淋第2支也只要10元優惠;7-11久違的自有品牌茶飲優惠終於等到了!烏龍茶550ml四瓶只要40元,平均特價10元,喜歡喝
2024-04-25 07:55
-

天氣預報/猛烈雷雨到週日!「這兩天」最恐怖 吳德榮:慎防致災
近期台灣受到滯留鋒影響,降雨頻繁,氣象署今(25)日一早針對苗栗以南等西部10縣市發布大雨特報,對台南市、高雄市、屏東縣則是發布大雷雨即時訊息。氣象專家、中央大學大氣系兼任副教授吳德榮表示,今(25)
2024-04-25 07:39
全球
更多全球-
涉嫌海外補貼!歐盟突襲搜查中企 北京氣炸喊:堅決維護正當權益
歐盟委員會執法機關23日突襲搜查一間中國企業,位於荷蘭及波蘭的辦公地點,中國安檢設備生產商「同方威視」(Nuctech)24日證實,遭搜查的就是該公司,此事引起北京強烈不滿,揚言會盡力維護中企在歐權利
2024-04-25 08:35
-

遭美國要求「不賣就禁」!TikTok執行長放話:哪也不去、會告到底
美國國會本月表決通過熱門短影音平台Tiktok的「去中國化」法案,要求TikTok與其中國母公司「字節跳動」(ByteDance)分道揚鑣,「字節跳動」需於9個月內出售在美國的資產,否則TikTok將
2024-04-25 07:34
-

麻生太郎見川普 矢板明夫:日本不排除兩面壓寶、台灣可早做準備
日本執政黨自民黨副總裁、前首相麻生太郎,本週前往美國,在紐約與美國前總統川普(Donald Trump)會面,2人在曼哈頓的(Trump Tower)進行了約1個小時的會談,討論了美日同盟對印太地區安
2024-04-25 06:44
-

美企陸續發財報!美股漲跌互現、特斯拉飆升12% 市場還關注2數據
儘管部份美企隨著公布業績、財報後股價看好,但投資者對地緣局勢惡化的擔憂並未消失,美股主要指數週三個別發展,漲跌不一。綜合外媒報導,電動車巨頭特斯拉(Tesla)在其財報發布後股價飆升,收漲約12%,執
2024-04-25 06:13