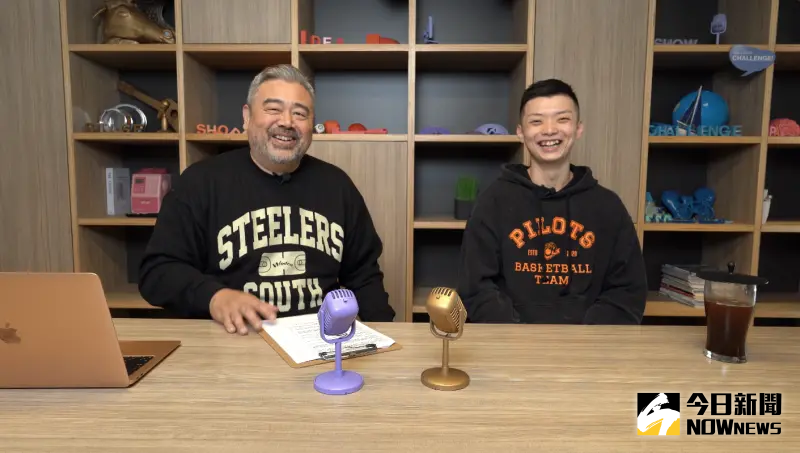
《鄉民大學問EP.38》精彩片段|台電頻跳電 原因竟是小鳥犯的錯?!理由讓萬美玲都傻眼!廢死交由公投?民調藍白死亡交叉 加總才大於綠!黃暐瀚獻這一計!拼這議題2028可翻轉!|NOWnews
NOW影音
更多NOW影音焦點
更多焦點-

司委會表決散會!吳思瑤嘆:國民黨認真撐不過3小時
立法院司法法制委員會今(25)日進行國會改革法案審查,最終國民黨在下午5時許提出散會動議並以5比4通過,對此民進黨立法院黨團幹事長吳思瑤嘆,國民黨認真果然撐不了3小時,又提散會動議沒收法案審查,而傅崐
2024-04-25 19:09
-

拋橄欖枝?哈馬斯官員:若讓巴勒斯坦「獨立建國」願解除武裝
以巴衝突持續,加薩地區遲遲不見和平曙光,各界期盼的停火協議遙遙無期。對此,《美聯社》今(25)日報導指出,哈馬斯(Hamas)高級官員哈亞(Khalil al-Hayya)透露,如果巴勒斯坦能夠完成獨
2024-04-25 19:18
-

《淚之女王》金智媛結婚現場!韓劇CP御用飯店 玄彬孫藝真也愛這
金秀賢、金智媛搭擋的Netflix韓劇《淚之女王》,開播後一路維持高收視率,目前距離tvN電視台收視率第一的紀錄僅一步之遙。本週末《淚之女王》將播出完結篇,讓不少粉絲都十分期待金秀賢與金智媛這對CP可
2024-04-24 17:39
-

又有偷拍狼!才藝班負責人硬碟驚見「女童如廁照」 至少2人受害
新北市某才藝班日前遭家長檢舉,范姓負責人(65歲)涉嫌偷拍女童如廁,雖警方第一時間拘提偵辦,但礙於當時未發現證據,檢方只能以2萬元交保,近日警方順利還原查扣的相機及電腦硬碟,發現至少有2名學童受害,昨
2024-04-25 19:02
精選專題
要聞
更多要聞-

司委會表決散會!吳思瑤嘆:國民黨認真撐不過3小時
立法院司法法制委員會今(25)日進行國會改革法案審查,最終國民黨在下午5時許提出散會動議並以5比4通過,對此民進黨立法院黨團幹事長吳思瑤嘆,國民黨認真果然撐不了3小時,又提散會動議沒收法案審查,而傅崐
2024-04-25 19:09
-

徐巧芯大姑涉詐騙洗錢 王世堅:代表政府打詐有一定成效
國民黨立委徐巧芯大姑與其丈夫涉入詐騙洗錢案,對此民進黨立委王世堅今(25)日表示,從徐巧芯家人的詐騙案就可以知道,政府打擊詐騙還是有一定成效,認為一切等司法調查就會有結果,徐巧芯現在講的都只是欲蓋彌彰
2024-04-25 18:24
-
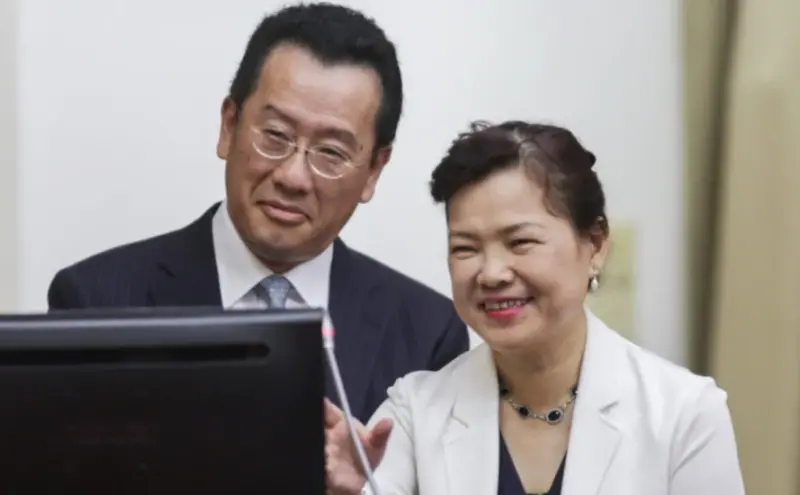
王美花與顧立雄從班對到政治夫妻!30年婚姻仍保甜蜜:全靠怕老婆
經濟部長王美花與老公顧立雄是知名的政治界夫妻檔,近日隨著520準總統賴清德將就職,內閣也迎來交接。顧立雄將出任國防部長,而王美花傳言將接下台新金控的獨立董事。兩人當年是台大法律系班對但個性差別大,王美
2024-04-25 18:16
-

傅崐萁、黃國昌不在也沒差!藍委提散會動議 再度「沒收」委員會
立法院司法法制委員會今(25)日繼續審查民進黨團提出的國會改革相關法案,藍綠原本一團和氣,理性討論,但下午2點繼續開會進行逐條討論時,漸漸有火藥味,加上藍委認為召委鍾佳濱主持議事不公,最後再度提散會動
2024-04-25 18:03
新奇
更多新奇-

24歲台妹當性工作者!驚爆「每月薪水60萬」:台灣8成男人買過春
台灣知名脫口秀演員曾博恩昨(24)日推出新節目《初識啦!阿博》,試播集題材就相當辛辣,找來24歲的性工作者女子以及男友進行訪談,對方更驚爆「每月薪水60萬」,並認為台灣有8成男人買過春。▲可愛表示,現
2024-04-25 15:05
-
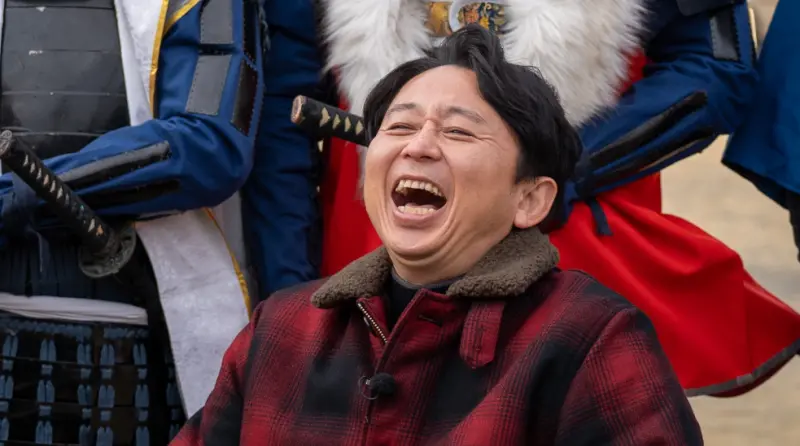
被《關鍵時刻》誤認成東大教授!有吉弘行看到了 本人回應超幽默
台灣政論節目《關鍵時刻》,由知名主持人劉寶傑領銜,時常針對各種時事進行語氣激昂的講解。不過近期在談論423地震話題時,誤將日本知名諧星主持人有吉弘行當成日本東京大學地震權威教授笠原順三,截圖瞬間在網路
2024-04-24 22:31
-
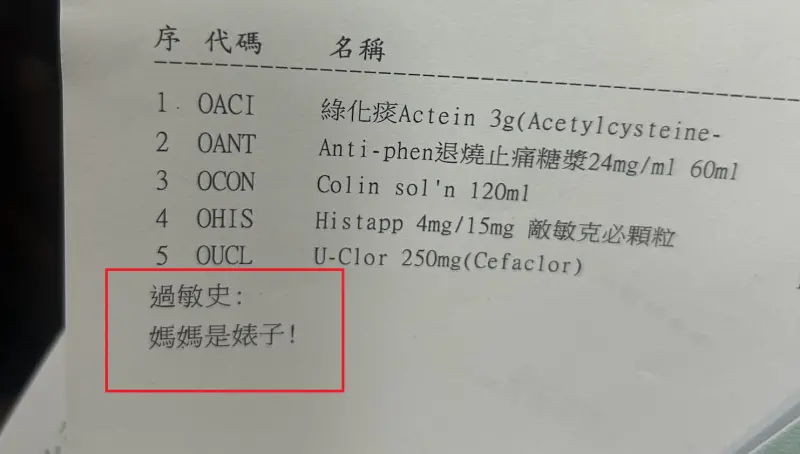
基隆醫院藥單上標註「媽媽是婊子」!人妻一看傻眼 護理師急道歉
(更新時間10:10)一位媽媽今(24)日帶著孩子前往衛生福利部基隆醫院看診,沒想到拿到藥單時,卻看到上面過敏史竟寫上:「媽媽是婊子!」讓她當場傻眼,詢問醫院究竟是怎麼回事,護理師同樣納悶,也立刻向她
2024-04-24 21:09
-

世界100大美食最新排行曝光!台灣竟成「吊車尾」:連英國都輸了
許多國際遊客來台一定會品嘗珍奶、小籠包、雞排、滷肉飯,甚至勇敢一點的還能嘗試看看臭豆腐。卻有國際美食榜單,將台灣美食排名列在榜單末端,甚至還有頗具權威性的美食評論刊物,2023年度最新榜單只給台灣第7
2024-04-24 18:43
娛樂
更多娛樂-

劉涵竹長9公分子宮肌瘤「與它和平共處」 會不會影響生育這樣說
42歲前主播劉涵竹去年3月做健檢時,發現子宮長6顆息肉還有9公分大的肌瘤,已經壓迫到膀胱,她今(25)日主持「響應『2024國際玫瑰斑月』避免玫瑰斑復發」活動,透露治療後子宮肌瘤已經縮小,目前與病灶和
2024-04-25 18:00
-

Selina「懷雙胞胎3個月」真相曝光!夢想成真當三寶媽:拚到停經
Selina生下兒子小腰果之後代言接不停,今(25)日出席孕產護理品牌代言活動,提到想要生第二胎這件事情,她坦言目前還沒有達成,但透露最近有夢到「胎夢」,夢裡面醫師告訴她懷了「雙胞胎」3個月:「我會拚
2024-04-25 17:25
-

張小燕被黃子佼害慘!許富凱公開兩人私訊內容:她不想要晚輩擔心
黃子佼涉嫌對年輕女孩伸狼爪、購買未成年少女不雅影片,負面形象波及恩師張小燕,她坦言後悔讓孟耿如嫁給黃子佼,心碎表示「一輩子沒有這樣怕見人」,至今沒公開露臉,與張小燕有私交的金曲台語歌王許富凱,今(25
2024-04-25 17:10
-

孫盛希緋聞男友KIRE「1分鐘激戰片段」流出!火辣女模正面曝光
孫盛希緋聞男友、潮流音樂人KIRE凱爾,在新歌〈dont stop〉MV當中化身「禁忌情人」,與火辣女模上演大尺度激吻戲,騎乘式深吻、十指緊扣深吻、濕身深吻樣樣來,在影片中連續激吻長達1分鐘,創下MV
2024-04-25 16:32
運動
更多運動-

射箭/湯智鈞關鍵10分箭!大逆轉 中華隊險勝義大利、收下銅牌
中華射箭反曲弓男團傳捷報!2024射箭世界盃今(25)日在上海站開打,台灣三少湯智鈞、林子翔、戴宇軒在八強賽時力退地主中國隊,雖在準決賽時不敵南韓,不過銅牌戰在加射階段,靠著「湯包」湯智鈞1支關鍵10
2024-04-25 18:19
-

「法國跑車」Tony Parker抵台!與NBA傳奇Wilkins熱情幫粉絲簽名
前聖安東尼奧馬刺球星「法國跑車」Tony Parker以及亞特蘭大老鷹傳奇名將Dominique Wilkins今(25)日正式搭機抵台,他們將在明日舉辦抵台記者會,並將於4月26日至28日,參加在國
2024-04-25 17:29
-

中職/Lamigo「同樂會」回娘家 樂天本季桃園主場首戰、巧遇台鋼
樂天桃園棒球場明(26)日將迎來本季首戰,對上由洪一中領軍的台鋼雄鷹,這是「大王」王柏融自2018年10月13日後,睽違5年6個月再度回到這座熟悉的球場,令不少球迷相當期待。這場三連賽的系列戰桃園球場
2024-04-25 17:23
-

利物浦0:2爆冷輸艾佛頓!輸掉英超爭冠希望 兵工廠、曼城搶冠軍
英超聯賽利物浦在今(25)日補賽爆冷以0:2敗給同城死敵艾佛頓,加上兵工廠先前5:0大勝切爾西,而曼城即將於26日凌晨3點對上布萊頓,目前兵工廠、利物浦和曼城積分已經拉開差距,其中利物浦想要實現英超冠
2024-04-25 16:19
財經生活
更多財經生活-

半導體封測大廠京元電明暫停交易 重大訊息待公布
半導體封測大廠京元電今 (25) 日公告,因有重大訊息待公布,經證交所同意,上市普通股及以其為標的之認購 (售) 權證也同時暫停交易,待前開重大訊息公布後,再申請恢復交易,業界認為應與財報或併購有關。
2024-04-25 18:55
-

天氣預報/明天雨更猛!連2天雷雨「全台躲不過」 中南部防水災
明(26)日起至週六是這波鋒面雨勢最猛烈的時刻,各地都有降雨機會,尤其是中南部要留意豪雨致災,注意短延時強降雨伴隨雷擊和強陣風,劇烈降雨會持續到週六白天,入夜後降雨逐漸緩和,不過鋒面帶來的降雨會影響到
2024-04-25 18:46
-

花蓮強震後餘震不斷!4/23單日飆194起地震 專家:將持續晃3個月
4月3日花蓮7.2大地震後,餘震截至目前仍一波接著一波,讓不少民眾相當憂心,從中央氣象署提供的逐日統計圖可發現,雖餘震次數逐日遞減,不過4月23日卻突飆194起地震,對此中央氣象署表示,雖然我們無法預
2024-04-25 18:13
-

長期投資基金好、還是ETF好?台股基金短中長期都完勝
長期投資該買台股ETF?還是台股基金?根據晨星資料統計,規模前10大台股基金無論近1年、近2年、近3年、近5年、近10年的平均績效表現都優於台股ETF,而且投資時間越長,報酬率勝出的幅度越大。以近3年
2024-04-25 17:56
全球
更多全球-

打破紀錄!阿根廷環球小姐地區賽 60歲「美魔女」律師奪冠
阿根廷近日展開環球小姐地區選拔賽,在布宜諾斯艾利斯的地區賽中,一名美魔女律師打破年齡紀錄,以60歲的年紀勇奪后冠,將在5月與來自全國的佳麗一同競逐代表阿根廷參賽的資格。綜合外媒報導,在阿根廷一場環球小
2024-04-25 18:05
-

人力遭取代!印度IT專家:客服中心一年後會被AI「殺死」
AI人工智慧的技術應用是否會取代人力,一直是各行各業討論不斷的話題。對此,印度IT業者塔塔諮詢服務公司(Tata Consultancy Services)的執行長克里斯瓦桑(K Krithivasa
2024-04-25 17:57
-

影/鱷魚闖美空軍基地扮飛機「輪擋」 被五花大綁帶走
美國佛州佛羅里達州坦帕的麥克迪爾空軍基地,近日一隻短吻鱷悄悄闖入,未料,這隻鱷魚還躲到一架KC-135加油機的機輪下,看似成為「輪擋」,有趣畫面掀起網友熱議,空軍基地隨即聯絡當地動保單位,相關人員五花
2024-04-25 17:11
-

全球首例!威尼斯今起徵收「入城費」 居民抗議:樂園才會收門票
義大利旅遊勝地威尼斯今(25)日起開徵「入城費」,進入市中心必須繳交5歐元、約175元新台幣的費用,當地居民、通勤上班族、學生和14歲以下的兒童以及過夜的遊客均可豁免,換言之,入城費是針對一日遊的遊客
2024-04-25 17:01