《鄉民大學問EP.37》字幕版|台南政治版圖有變數?謝龍介有機會?黃偉哲全說了!台南市長前哨戰開打!陳亭妃、王定宇、林俊憲鴨子划水 邱明玉揭他勝算高!黃智賢轉綠?被哥哥盜帳號?黃偉哲霸氣回應現場笑翻!
NOW影音
更多NOW影音焦點
更多焦點-

白委提議頭盔抗彈實彈測試 王定宇笑回:只要不是我當靶都可安排
美國軍事Youtuber「山姆小叔Gun Fun」去年在頻道針對國軍抗彈板進行測試,引發熱議。民眾黨立委林憶君今(24)日針對抗彈頭盔安全性及其標準提出質疑,並提議外交及國防委員會安排到兵試場做防護測
2024-04-24 17:12
-

俄國防副部長涉嫌收賄被捕!最高面臨15年刑期 遭控大發戰爭財
俄羅斯副國防部長伊凡諾夫(Timur Ivanov)週二因涉嫌收受巨額賄款遭到拘留,根據調查委員會說法,最高可判處15年有期徒刑,但是調查委員會尚未提供伊凡諾夫收賄案情的細節。這是俄烏戰爭以來,俄羅斯
2024-04-24 17:05
-

《不夠善良的我們》林依晨討好型人格挨轟綠茶 許瑋甯心疼發聲
在台劇《不夠善良的我們》裡,林依晨討好型人格作祟,趁賀軍翔與許瑋甯感情破裂,從「紅粉知己」順勢扶正成功,被網友形容為「綠茶婊」或「小三」,但許瑋甯視角並非如此,她表示,「簡慶芬是一個很多事情都想要做到
2024-04-24 13:54
-

全運會台北田徑場驚傳火警!觀眾席突竄大量白煙 消防員緊急救援
全國中等學校運動會今(24)日在台北田徑場舉辦賽事,沒想到過程中觀眾席疑似電線走火,瞬間竄出大量白煙,所幸工作人員見狀緊急拿出滅火器救災,警消趕抵前已順利撲滅,詳細起火原因還有待進一步釐清。
2024-04-24 16:45
精選專題
要聞
更多要聞-

白委提議頭盔抗彈實彈測試 王定宇笑回:只要不是我當靶都可安排
美國軍事Youtuber「山姆小叔Gun Fun」去年在頻道針對國軍抗彈板進行測試,引發熱議。民眾黨立委林憶君今(24)日針對抗彈頭盔安全性及其標準提出質疑,並提議外交及國防委員會安排到兵試場做防護測
2024-04-24 17:12
-

徐巧芯粉絲寄威脅信?謝佩芬分享經驗:講到真話與痛處才會收到
國民黨立委徐巧芯大姑捲入詐騙洗錢案,民進黨立委黃捷、台北市議員苗博雅針對此事向徐巧芯提出許多質疑,近日卻傳出兩人陸續收到恐嚇信,內容都是「若再造謠徐巧芯,將被炸死」目前兩人都已報警處理。民進黨前發言人
2024-04-24 17:08
-

8成民意反廢死 他獻策立院對抗到底:不信賴清德影響不了大法官
憲法法庭23日針對死刑是否違憲案進行言詞辯論,大法官詹森林說,難道大法官不能做憲法教育或裁判,「一定要跟民眾的意見妥協嗎?」引起關注。對此,前立委郭正亮認為,現在有8成民意反對廢死,若最後大法官真的做
2024-04-24 17:04
-

公司以宿舍名義買豪宅「員工僅1人」!黃國昌怒:內政部竟核准
去年修正《平均地權條例》並新增私法人購屋許可制。民眾黨立委黃國昌今天在立院踢爆,一堆投資公司用「宿舍」當作名義去買豪宅,員工只有1人,內政部竟然也許可?對此,內政部長林右昌坦言「這不應該,這是在鑽漏洞
2024-04-24 16:53
新奇
更多新奇-
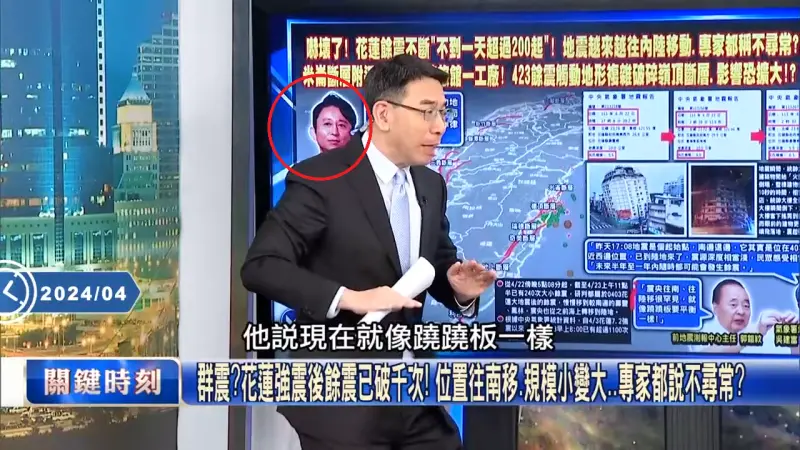
劉寶傑《關鍵時刻》誤植「有吉弘行」照片!粉絲笑翻:變地震專家
知名政論節目主持人劉寶傑所主持的《關鍵時刻》,因為語氣激昂的強烈風格,深獲許多民眾的喜愛。日前更因為談論天團BTS(防彈少年團)金泰亨入伍的片段,因此在南韓爆紅。不過沒想到近期《關鍵時刻》節目組卻在談
2024-04-24 13:39
-

別管60元便當了!全聯「買1水果」送保鮮盒 優惠瘋傳:錯過等1年
先別管60元便當了!全聯福利中心因為經常推出許多新品,或者是期間限定的產品,因此婆媽常常會在臉書社團上討論分享。然而近日就有不少人分享去全聯購買「寶石紅奇異果」,並且開箱分享口感,沒想到卻釣出內行婆媽
2024-04-24 11:57
-

王彩樺是「台灣諧音始祖」!12年前神講解爆紅 觀眾挖出影片服她
相信有不少人之都知道台灣人真的非常愛用諧音,不過是餐廳、手搖飲甚至是健身房的名字,都能利用諧音來取名,像是知名連鎖飲料店「可不可(渴不渴)」、「鶴茶樓(喝茶嘍)」都是諧音。然而,近日就有網友挖出國民岳
2024-04-24 10:53
-

《池水抽光好吃驚》來台灣!抽光中興湖 驚見「激似鯊魚」外來種
日本知名綜藝節目《池水抽光好吃驚》在今年3月份來台灣,由主持人田村淳與興大生組成多達1百人的「池水台日隊」,抽光國立中興大學內的「中興湖」池水,結果捕撈出近3百隻生物,裡面甚至還有「激似鯊魚」的外來種
2024-04-23 18:07
娛樂
更多娛樂-

F.I.R.當年多紅?CD爆賣30萬張威脅雙J 阿沁曾公開要前女友歸隊
4月23日是F.I.R.飛兒樂團出道20週年,吉他手阿沁昨(23)日發文許願:「希望建寧老師、詹雯婷,不要再吵架了!」期盼兩位戰友合約官司和平落幕,2034年3人合體於台北大巨蛋舉辦演唱會。F.I.R
2024-04-24 17:00
-

最殺男團Energy合體再爆喜訊!7/28加場開唱 27日搶票規則1次看
「最殺唱跳男團」Energy復出後的首場《一觸即發》台北小巨蛋演唱會,日前開賣之後就秒殺售完,今(24)日也宣布將於7/28加場,27日上午11點搶先開賣,阿弟開心表示:「希望這次大家都能買到票,加油
2024-04-24 16:40
-

女團ILLIT再惹議!針織裙透視少女蜜大腿 粉絲怒:影片令人驚嚇
韓國知名經紀公司HYBE旗下的「BELIFT LAB」近期推出全新女團ILLIT,上月底推出的出道曲〈Magnetic〉一公開就空降美國告示牌音樂榜全球200大,洗腦的旋律加上可愛的「手指舞」吸引不少
2024-04-24 16:13
-

木村拓哉《Believe》大啖平價壽司 粉絲瞬間湧入癱瘓店家官網
日本男神木村拓哉近日為最新日劇《Believe》宣傳,他帶著同劇演員齋藤工、竹內涼真一起上綜藝節目,3人一邊品嘗迴轉壽司,一邊要齊力猜出該店的人氣商品TOP10,有趣的是,節目還沒播完,店家就突然透過
2024-04-24 15:46
運動
更多運動-

NBA季後賽/快艇Leonard急於復出卻淪為戰犯!正負值-8全隊最爛
NBA洛杉磯快艇今(24)日在季後賽首輪G2,於主場迎戰達拉斯獨行俠,獨行俠靠著Luka Doncic與Kyrie Irving合砍55分,以96:93拿下勝利。本場快艇輸球的頭號戰犯,無疑是傷癒復出
2024-04-24 16:36
-

快訊/大雨侵襲!中職新莊球場台鋼雄鷹與富邦悍將之戰宣布延賽
台鋼雄鷹今(24)日宣布,今日4/24原定跟富邦悍將新莊例行賽,因連夜大雨,場地不適合進行比賽,確定延賽,補賽日期未定。富邦昨日以4:1擊敗台鋼,不過今天上午大雨滂沱,因此場地不適合比賽。中職聯盟也正
2024-04-24 14:56
-

NBA快評/太陽崩盤三大主因 Booker被爆賽前找「玩偶姊姊」紓壓
季前被視為是奪冠大熱門的太陽,在季後賽首輪苦吞二連敗,且華麗「三核心」進攻組合Devin Booker、Kevin Durant、Bradley Beal似乎有心無力,連兩戰團隊得分都未達100,且輸
2024-04-24 14:31
-

英超/阿森納5:0大勝切爾西!領先曼城、利物浦 兵工廠有望奪冠
英超第29輪的補賽,「兵工廠」阿森納主場面對「切爾西,上半場,賴斯助攻特羅薩德小角度精采進球,傑克森射門中柱,隨後門前又錯失頭球機會,半場阿森納1球領先。然而90分鐘比賽結束,阿森納交出了一場難以置信
2024-04-24 13:35
財經生活
更多財經生活-

房屋稅5月開徵!全台逾944萬件、稅額911億 7大繳稅方式一次看
今(113)年期房屋稅將5月1日開徵,繳納期限至5月31日,全國開徵944.64萬件、年增1.66%,稅額新台幣911.17億元、成長4.74%,光6都開徵件數就占逾7成,其中件數以新北市最多有181
2024-04-24 17:02
-

7-11勞動節優惠偷跑!美式、珍珠奶茶買1送1 咖啡買51送51可寄杯
7-11迎接迎接4月30日國際珍奶日與5月1日勞動節,優惠提早從4月底開跑,限時推出咖啡、飲品優惠,包括4月26日起有「CITY PEARL」珍珠全品項同價位任選買1送1,還有4月29日至5月1日限時
2024-04-24 16:32
-

稱霸南臺灣的國宴級美味!從赤崁到國際 揭露這杯台灣之光的秘密
「等一下要喝什麼?」這絕對是上班族必問的問題,辛苦工作之餘來一杯奶茶,絕對是每天上班療癒心靈的日常。不過說到奶茶,就不得不提到1986年創立的翰林茶館,如今已發展成為擁有超過40間分店的知名品牌,結合
2024-04-24 16:29
-
變頻冷氣「內行不只會裝日立」!老闆招了2品牌:師傅之間的秘密
炎炎夏日即將到來,家裡的冷氣也準備要開工動起來!不少人最近都準備開始清潔家中冷氣,或是汰換家中老舊冷氣,以因應下個月天氣開始變熱的天氣。那麼每次只要說到變頻冷氣,大家不是想到「大金」就是「日立」,難道
2024-04-24 16:23
全球
更多全球-

俄國防副部長涉嫌收賄被捕!最高面臨15年刑期 遭控大發戰爭財
俄羅斯副國防部長伊凡諾夫(Timur Ivanov)週二因涉嫌收受巨額賄款遭到拘留,根據調查委員會說法,最高可判處15年有期徒刑,但是調查委員會尚未提供伊凡諾夫收賄案情的細節。這是俄烏戰爭以來,俄羅斯
2024-04-24 17:05
-

赴日注意!觀光客擬改為「先付全額再退稅」 1招防混亂簡化程序
赴日旅遊的民眾注意了,日本政府為了遏止國內非法轉賣免稅商品、惡意逃漏稅等行為,正在研議變更觀光客免稅制度,改成「先付款、後退稅」,外國旅客購物時先行支付消費稅,出境時再於機場辦理退稅,而為了簡化機場退
2024-04-24 16:04
-

海運飆風再起?地中海港口示警:貨櫃快滿出來了
全球海運飆風再起?隨著各大貨櫃航商因躲避葉門胡塞武裝攻擊而繞道好望角,地中海各港口也面臨考驗,外媒報導,地中海西部周圍多個貨櫃港口已幾近滿載,增加歐洲零售業者與製造商面臨庫存成本增加和零組件短缺的風險
2024-04-24 15:08
-
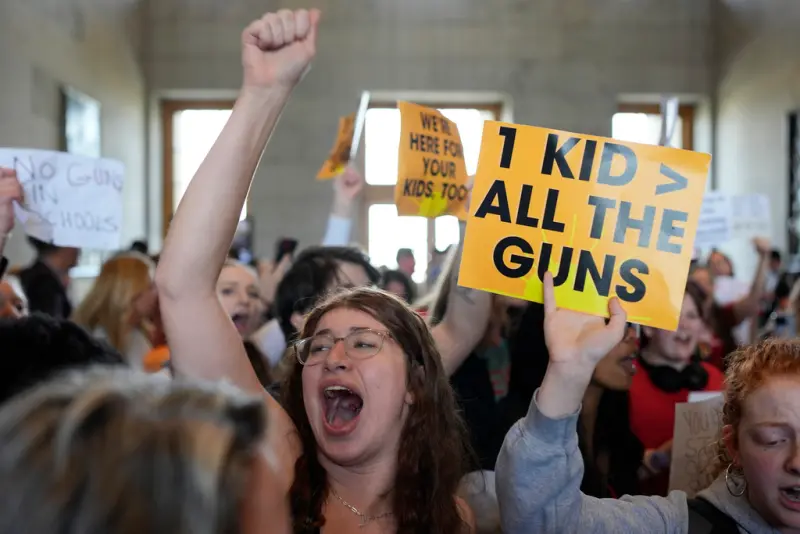
以暴制暴?美田納西州「允老師攜槍入校」以阻槍擊 抗議者批瘋狂
美國田納西州首府納希維爾(Nashville)去年3月爆發重大校園槍擊案,造成3名孩童和3名成人死亡。槍擊案後各界呼籲管制槍枝,不過,田納西州參議院週二通過一項「教師武裝法案」,允許符合資格的教師和學
2024-04-24 14:34